
FerrumGate
Identity and Access Management (IAM)
Commercial Alternatives
Key Features
Zero Trust Network Access (ZTNA) gateway
Implements zero trust security model by verifying every connection request regardless of location or device, ensuring no implicit trust and requiring explicit verification for all network access attempts.
Device identity and posture assessment
Continuously evaluates device security posture including patch status, antivirus updates, and compliance with organizational policies before granting network access, ensuring only secure devices connect to resources.
Multi-factor authentication and conditional access
Enforces strong authentication requirements with support for multiple factors including TOTP, FIDO2, and biometrics, with conditional access policies based on user, device, location, and risk factors.
Micro-segmentation and least privilege access
Implements granular network segmentation ensuring users and devices can only access specifically authorized resources, reducing attack surface and containing potential security breaches.
Real-time monitoring and session recording
Provides comprehensive visibility into user activities with session recording, command logging, and real-time monitoring capabilities for privileged access sessions and sensitive resource interactions.
Cloud-native architecture with API-first design
Built for cloud environments with RESTful APIs enabling integration with existing security infrastructure, identity providers, and automation platforms for streamlined operations and management.
Pros and Cons
Pros
Open source
Free open source ZTNA solution
Multi-factor authentication
Built-in MFA capabilities
Flexible deployment
Can be deployed on-premises or in the cloud
Granular access control
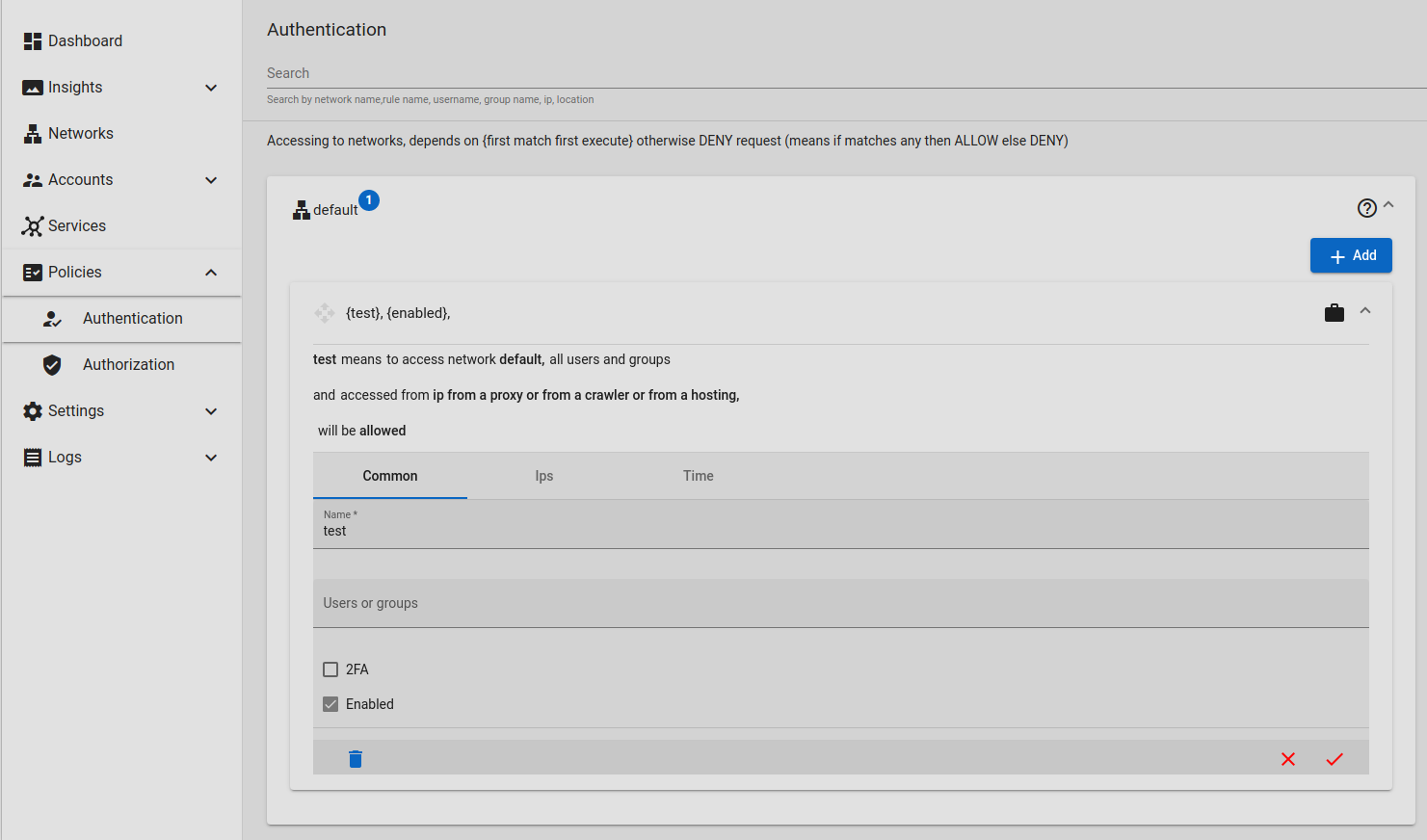
Detailed access policies and controls
Cost-effective
Lower total cost of ownership than commercial alternatives
Cons
Limited community
Smaller community compared to other open source security tools
Documentation gaps
Less comprehensive documentation than commercial alternatives
Integration limitations
Fewer pre-built integrations with enterprise systems
Support challenges
Limited professional support options
Feature Comparison
Comments
Matthew Evans • SecureLink MSP
Jun 25, 2025
Solid zero trust network solution
Ayumi Nakamura • CloudBridge MSP
Jun 22, 2025
Good for modern security needs
Joshua Fisher • CloudSecure MSP
Jun 19, 2025