
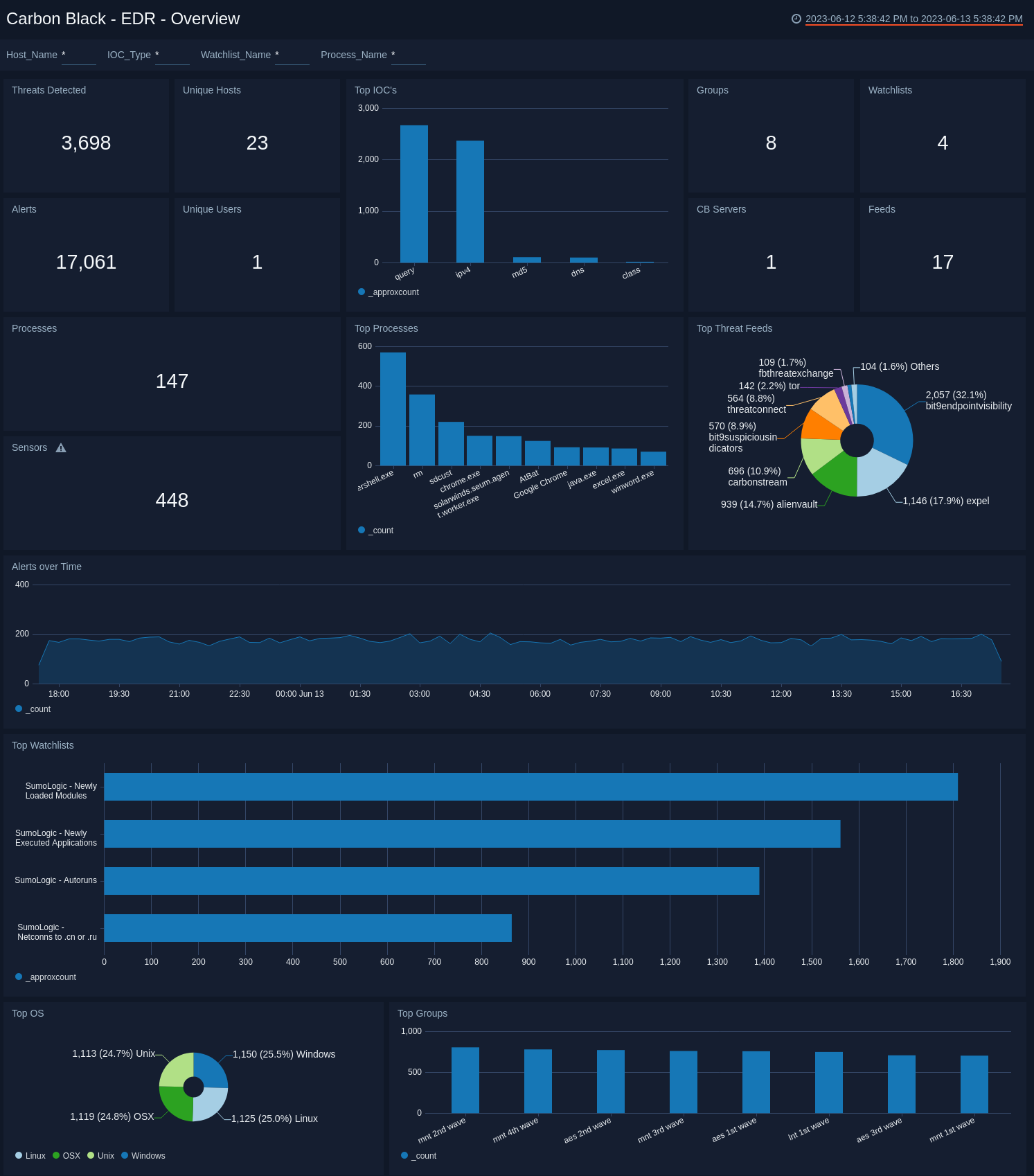
Carbon Black
Endpoint Detection and Response (EDR)
Alternative Vendors
Commercial Alternatives
Key Features
Next-Generation Antivirus
Machine learning and behavioral analytics detect and block malware, including zero-day threats and advanced persistent threats without relying solely on signatures.
Endpoint Detection and Response
Real-time visibility into endpoint activities with advanced threat hunting capabilities, incident response automation, and detailed forensic analysis.
Cloud-Native Architecture
Analyzes over 1 trillion security events daily to proactively uncover attacker behavior patterns and provide real-time threat intelligence.
Application Control
Whitelisting, blacklisting, and greylisting capabilities control application execution, reducing attack surface and preventing unauthorized software.
Workload Protection
Secures servers and cloud workloads with vulnerability management, runtime protection, and compliance enforcement across hybrid environments.
Pros and Cons
Pros
Advanced Threat Detection
Superior zero-day threat protection using machine learning and behavioral analysis, significantly better than traditional signature-based solutions
Comprehensive Visibility
Excellent forensic capabilities and detailed endpoint activity monitoring providing deep insights into security incidents
Easy Management
Intuitive web-based console with straightforward deployment and management, suitable for IT teams of varying skill levels
Scalable Architecture
Cloud-native design scales easily from small businesses to large enterprises without infrastructure concerns
Cons
High False Positives
Predictive nature results in many legitimate processes being blocked, especially during initial learning period and environment setup
Resource Intensive
Can cause performance issues on older systems due to continuous monitoring and behavioral analysis requirements
Expensive Pricing
Higher cost compared to traditional antivirus solutions, making it less accessible for smaller organizations with limited budgets
Complex Configuration
Advanced features can be difficult for less experienced IT teams to configure properly, potentially leading to misconfigurations
Feature Comparison
Comments
No Comments Yet
Be the first to share your experience with Carbon Black.